AI tools for cybersecurity and ethical hacking are reshaping digital defense by providing faster, smarter, and more adaptive ways to detect and mitigate threats. From autonomous threat monitoring and intelligent security operations to continuous security validation and proof-based exposure testing, these solutions help security professionals stay ahead of increasingly sophisticated cyberattacks. AI models analyze massive amounts of traffic, endpoint behavior, identity signals, and threat intelligence to uncover patterns that human teams may miss, enabling faster reaction times and fewer false positives. Whether you're protecting a corporate network, hardening endpoints, securing cloud workloads, or running controlled internal security assessments, today’s AI-driven platforms support everything from detection and investigation to automated disruption and remediation workflows. In this guide, we explore the top AI cybersecurity tools—both paid and free—that improve resilience, support compliance, and help SOC teams and security leaders secure systems with speed, scale, and precision.

Top Paid AI Cybersecurity Tools
| Rank | Tool | Focus | Price | Best For |
|---|---|---|---|---|
| #1 | CrowdStrike Falcon | AI-powered EDR/XDR | From $7.99/device/month | Endpoints + SOC teams |
| #2 | Microsoft Defender XDR | Unified detection + response | Varies by licensing | Microsoft-first environments |
| #3 | SentinelOne Singularity | Autonomous endpoint + identity security | Custom pricing | Automated response at scale |
| #4 | Darktrace | Network/email AI threat detection | Enterprise pricing | Anomaly-based detection |
| #5 | Pentera | Automated security validation | Custom pricing | Continuous pentest-style validation |
CrowdStrike Falcon
CrowdStrike Falcon is a widely used, cloud-native endpoint security platform designed to stop modern attacks with fast behavioral detection, threat intelligence, and automated response. Its AI-driven analytics continuously evaluate activity across devices to identify suspicious patterns (like ransomware behavior, credential misuse, and stealthy persistence) without requiring heavy on-device performance overhead. For security teams, the real value is how Falcon turns noisy endpoint telemetry into actionable detections, investigations, and response steps that can be standardized across thousands of endpoints. Many organizations also use Falcon as the “front line” for incident response because it supports rapid containment actions (like isolating hosts) and streamlined triage workflows. It’s a strong fit for SOC teams that need enterprise-grade EDR/XDR capabilities, clear visibility, and scalable operations—especially in distributed environments with remote work, mixed operating systems, and high alert volume.
Microsoft Defender XDR
Microsoft Defender XDR brings unified detection and response across endpoints, identities, email, collaboration, and cloud apps—helping teams see the full attack chain rather than isolated alerts. Instead of treating every signal as a separate event, Defender correlates related activity into incidents and uses automation to prioritize what matters most. This is especially useful for organizations already invested in Microsoft 365 and Entra ID, because the platform can connect identity and device risk signals to reveal high-impact threats like credential theft, malicious inbox rules, and lateral movement attempts. Defender’s strength is operational efficiency: analysts can investigate incidents in one place, accelerate containment, and apply consistent policies across integrated Microsoft security controls. For many businesses, it’s a practical way to modernize a SOC without stitching together multiple vendor consoles—while still achieving strong coverage across the most common enterprise attack surfaces.
SentinelOne Singularity
SentinelOne Singularity is an AI-powered cybersecurity platform built around autonomous prevention, detection, and response. It’s best known for strong endpoint protection, but the broader platform also supports cloud, identity, and data security workflows through a unified console designed to reduce operational complexity. Singularity’s key advantage is speed: it can detect suspicious behavior quickly and trigger automated actions to stop threats before they spread, which is critical for ransomware and rapid “hands-on-keyboard” intrusions. For security teams, the platform aims to reduce alert fatigue with richer context and streamlined investigations, while still allowing expert analysts to dig into timelines and root-cause analysis when needed. If you want a modern, automation-first approach to endpoint defense—especially in environments where you need consistent coverage across many devices—SentinelOne is a strong option for scaling response and improving time-to-containment.
Darktrace
Darktrace focuses on anomaly-based cybersecurity using self-learning AI to identify unusual behavior across networks, cloud, email, and connected devices. Instead of relying only on signatures or static rules, it learns what “normal” looks like for your environment and then flags subtle deviations that may indicate phishing, insider threats, data exfiltration, or novel attack methods. One of the most appealing parts of the Darktrace approach is how it helps uncover threats that don’t match known patterns—particularly useful as attackers increasingly blend in with legitimate traffic. For security teams, Darktrace can act like an early warning system that highlights suspicious activity quickly, providing clear investigation trails to validate whether something is benign or malicious. It’s generally best suited for medium-to-large organizations that want additional AI-driven visibility and faster detection across complex, high-volume environments.
Pentera
Pentera is an automated security validation platform that helps organizations continuously test and prove real-world exposure—without relying solely on periodic manual penetration tests. It works by safely emulating attacker behavior across your environment to identify exploitable weaknesses, misconfigurations, and risky attack paths (for example, credential exposure and privilege escalation routes). The practical outcome is “proof-based” findings: security teams get a clearer view of what can actually be exploited, not just what might be vulnerable in theory. That makes it valuable for prioritization—helping teams focus remediation effort on issues that measurably reduce risk. Pentera is especially useful when you need repeatable validation after changes, patches, and control updates, and when leadership wants measurable improvements tied to exposure reduction. For organizations building a continuous exposure management program, it’s one of the strongest options for automated, scalable validation.
Top Free AI Cybersecurity Tools
| Rank | Tool | Focus | Limitations | Ideal Use |
|---|---|---|---|---|
| #1 | Wazuh | Open-source XDR + SIEM | Requires setup + tuning | Threat detection on a budget |
| #2 | Nmap + NSE | Network discovery | Manual scripting | Recon + scanning |
| #3 | Nuclei | Template-driven vulnerability scanning | Template management needed | DevSecOps + targeted checks |
| #4 | VirusTotal | File & URL scanning | Rate-limited API | Malware triage + reputation checks |
| #5 | TheHive | Incident response platform | Manual setup | SOC case management |
Wazuh
Wazuh is a popular open-source security platform that combines SIEM and XDR-style capabilities to help teams detect threats, monitor endpoints, and investigate suspicious activity without paying enterprise licensing fees. It collects security telemetry from endpoints and servers, correlates events, and helps surface indicators like unauthorized changes, suspicious processes, and policy violations. While Wazuh isn’t a “one-click AI SOC,” it’s highly automation-friendly and can be tuned to reduce noise and highlight meaningful detection patterns across a wide range of environments. The biggest tradeoff is effort: you’ll need to deploy agents, configure rules, and tune alerts to your environment for best results. For students, homelabs, startups, and cost-conscious IT teams, Wazuh is one of the best free foundations for building real monitoring and incident response workflows—especially when you want control, transparency, and the flexibility to grow your detection stack over time.
Nmap + NSE
Nmap remains one of the most trusted tools for network discovery, inventory, and security assessment. With the Nmap Scripting Engine (NSE), it becomes dramatically more powerful by enabling automated checks for services, misconfigurations, and known weaknesses during controlled assessments. While it’s not an AI product, it plays a key role in “AI-assisted” security workflows because it produces high-quality recon and verification data that security teams (and defensive automation) can act on. For example, NSE scripts can standardize routine validation tasks, accelerate baseline audits, and help identify exposure when environments change. Nmap is best used responsibly for scanning networks you own or have permission to test. If you’re learning cybersecurity, building internal security checklists, or validating how assets appear to your own security team, Nmap + NSE is a foundational free tool that stays relevant year after year.
Nuclei
Nuclei is a fast, modern vulnerability scanner that uses simple YAML templates to run targeted security checks across web apps, APIs, and infrastructure. Its template-driven design makes it highly adaptable: you can run focused scans for specific technologies, quickly add new checks, and standardize internal validation across teams. While it doesn’t “guess” vulnerabilities with generative AI, it is automation-first and pairs well with AI-assisted security processes because it produces consistent, repeatable results that can feed into triage and remediation workflows. The main limitation is that results quality depends on template selection and maintenance—so teams need to manage template sources and tune scanning to avoid noise. For bug bounty workflows, DevSecOps pipelines, and internal validation, Nuclei is a top free option when you want speed, control, and a practical scanning engine that can be tailored to your exact environment.
VirusTotal
VirusTotal is a widely used online service for checking suspicious files, URLs, domains, and IP addresses. It aggregates results from many security engines and reputation sources, helping you quickly assess whether something is likely malicious, potentially unwanted, or simply a false positive. For everyday security triage, it’s one of the fastest ways to get “second opinions” on a file hash or link before you take further action. It’s also useful for defenders who want additional context during investigations, such as historical detections and related artifacts. The free tier is easy to use through the web interface, but API access is rate-limited and advanced features are reserved for paid offerings. Even with those limits, VirusTotal remains a reliable free tool for rapid malware triage and link checking—especially when you’re validating alerts, analyzing suspicious email attachments, or reviewing potentially dangerous downloads.
TheHive
TheHive is a well-known incident response and case management platform that helps security teams track investigations, standardize response, and collaborate effectively during real incidents. Instead of losing context across chat messages and spreadsheets, teams can create structured cases, attach evidence, assign tasks, and maintain a clear timeline for every investigation. TheHive also integrates with enrichment workflows (often via companion tooling) so analysts can pull in threat intelligence and artifact context to speed up decisions. Like many open-source SOC tools, the tradeoff is setup: you’ll need to deploy it, configure integrations, and build the process that fits your team. If you’re building internal SOC maturity, training incident response workflows, or managing growing alert volume, TheHive is a strong free foundation for making response more consistent, auditable, and scalable—especially when you want visibility into “who did what, when” across investigations.
Rankings

Chatbots
AI chatbots have quickly evolved from simple assistants into powerful, multi-purpose tools used by millions of people every day...

Image Generators
AI image generators are revolutionizing the way creatives, marketers, and developers produce visual content by transforming text prompts into detailed, customized...

Writing Assistants
AI writing assistants have become indispensable tools for anyone who writes — from students and bloggers to business professionals and marketers...

Deepfake Detection
As deepfake technology becomes more advanced and accessible, detecting AI-manipulated content is now a critical challenge across journalism, education, law, and...
Productivity & Calendar
AI productivity and calendar tools have become essential for professionals, entrepreneurs, and students looking to make the most of their time without getting overwhelmed...

Natural Language To Code
Natural language to code tools are transforming software development by enabling users to build apps, websites, and workflows without needing advanced programming...
Blog
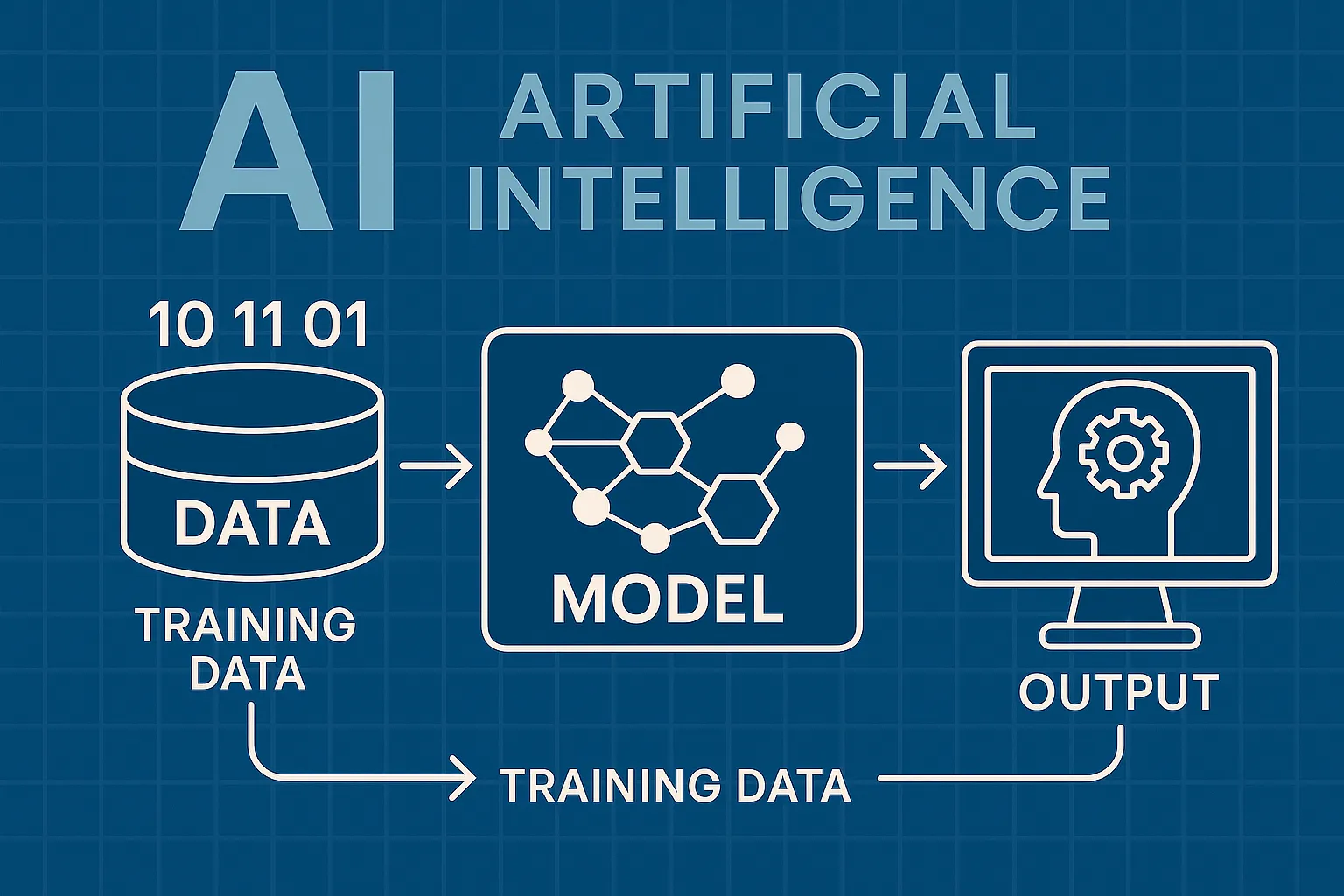
How AI Actually Works
Understand the basics of how AI systems learn, make decisions, and power tools like chatbots, image generators, and virtual assistants.

What Is Vibe Coding?
Discover the rise of vibe coding — an intuitive, aesthetic-first approach to building websites and digital experiences with help from AI tools.
7 Common Myths About AI
Think AI is conscious, infallible, or coming for every job? This post debunks the most widespread misconceptions about artificial intelligence today.

The Future of AI
From generative agents to real-world robotics, discover how AI might reshape society, creativity, and communication in the years ahead.
How AI Is Changing the Job Market
Will AI replace your job — or create new ones? Explore which careers are evolving, vanishing, or emerging in the AI-driven economy.

Common Issues with AI
Hallucinations, bias, privacy risks — learn about the most pressing problems in current AI systems and what causes them.